Managed IT Services: Customized Solutions for Your Business
Managed IT Services: Customized Solutions for Your Business
Blog Article
Exactly How Managed IT Solutions Can Enhance Your Firm's Cybersecurity and Safeguard Delicate Data From Dangers
In today's digital landscape, the protection of delicate data is extremely important for any kind of company. Managed IT remedies provide a critical technique to enhance cybersecurity by giving accessibility to customized experience and progressed technologies. By implementing tailored security strategies and conducting constant monitoring, these services not just safeguard against present risks but additionally adapt to a progressing cyber atmosphere. The inquiry remains: just how can companies efficiently incorporate these services to develop a durable protection against progressively innovative strikes? Discovering this additional discloses vital insights that can significantly affect your company's safety and security stance.
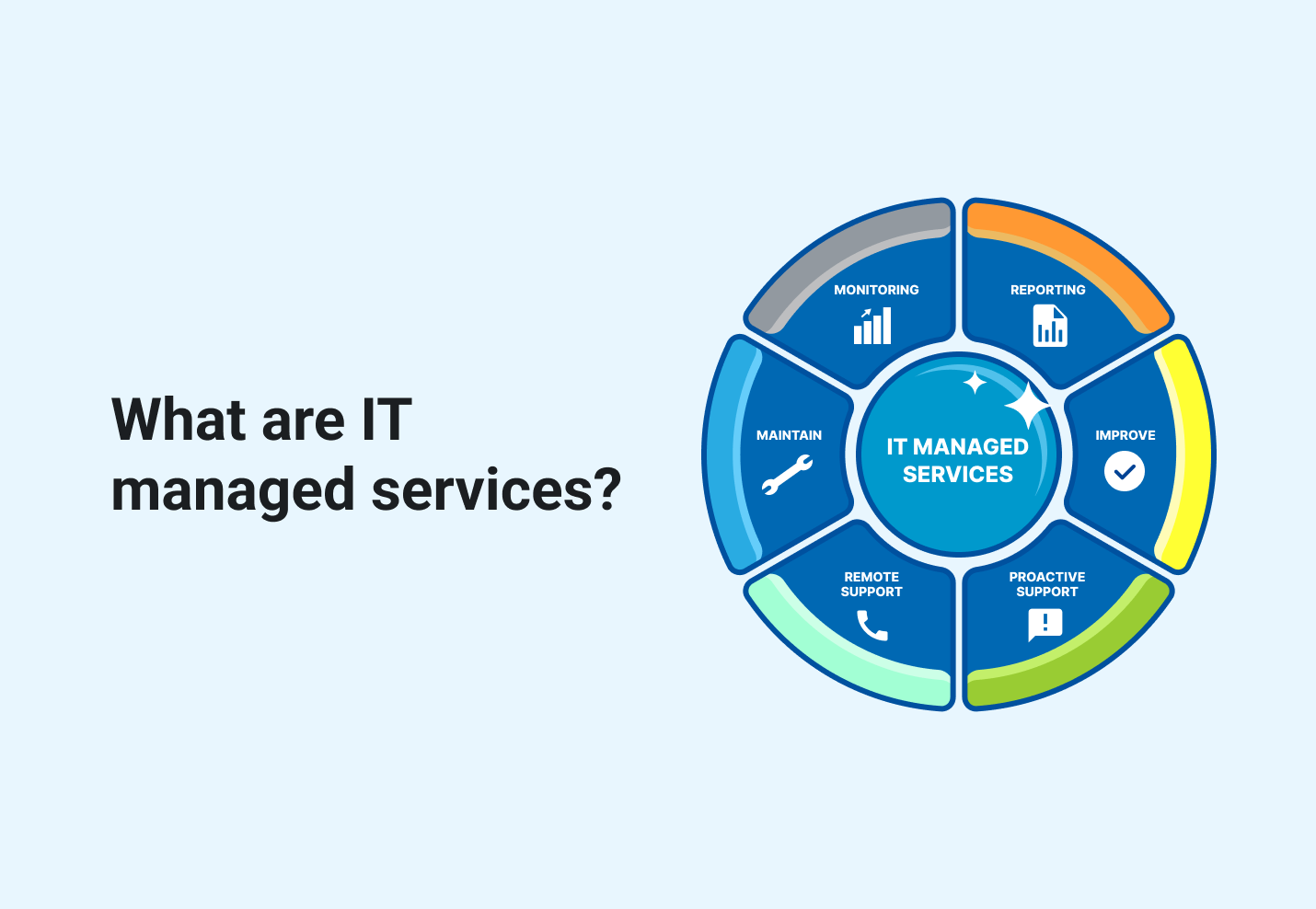
Comprehending Managed IT Solutions

The core philosophy behind handled IT options is the shift from reactive problem-solving to proactive management. By outsourcing IT responsibilities to specialized providers, companies can concentrate on their core competencies while making sure that their modern technology framework is effectively preserved. This not only improves functional performance yet also cultivates development, as organizations can assign sources in the direction of strategic campaigns rather than daily IT maintenance.
Furthermore, managed IT options assist in scalability, enabling firms to adjust to changing business needs without the concern of comprehensive in-house IT investments. In a period where data honesty and system integrity are vital, comprehending and implementing handled IT options is important for organizations looking for to take advantage of innovation successfully while protecting their operational continuity.
Trick Cybersecurity Perks
Handled IT services not just enhance operational performance however additionally play an essential role in strengthening an organization's cybersecurity posture. Among the main benefits is the facility of a robust protection structure tailored to particular company requirements. Managed Cybersecurity. These remedies usually consist of extensive risk evaluations, permitting organizations to determine susceptabilities and address them proactively

One more trick advantage is the integration of innovative security modern technologies, such as firewall softwares, breach detection systems, and file encryption methods. These tools operate in tandem to produce numerous layers of safety and security, making it significantly much more difficult for cybercriminals to penetrate the company's defenses.
Lastly, by outsourcing IT administration, business can allocate resources much more successfully, permitting inner teams to concentrate on tactical initiatives while making certain that cybersecurity continues to be a top priority. This all natural technique to cybersecurity inevitably protects delicate information and strengthens overall organization honesty.
Positive Danger Discovery
An effective cybersecurity technique rests on proactive threat detection, which enables companies to recognize and alleviate potential risks prior to they intensify into significant cases. Executing real-time monitoring options permits companies to track network activity continually, giving insights right into anomalies that might suggest a violation. By using sophisticated algorithms and device learning, these systems can identify between regular behavior and possible threats, enabling swift action.
Normal vulnerability assessments are one more essential part of aggressive hazard discovery. These assessments assist organizations determine weak points in their systems and applications, allowing them to remediate susceptabilities before they can be made use of by cybercriminals. Additionally, threat knowledge feeds play an important duty in keeping companies notified about arising threats, enabling them to readjust their defenses as necessary.
Worker training is additionally essential in promoting a culture of cybersecurity recognition. By furnishing personnel with the expertise to recognize phishing attempts and other social engineering strategies, companies can decrease the likelihood of successful attacks (MSPAA). Ultimately, an aggressive approach to danger discovery not just enhances a company's cybersecurity pose however also imparts self-confidence among stakeholders that delicate data is being properly shielded against progressing hazards
Tailored Safety And Security Approaches
Just how can organizations successfully safeguard their special properties in an ever-evolving cyber landscape? The answer hinges on the application of tailored safety strategies that align with certain organization demands and run the risk of profiles. Identifying that no two companies are alike, managed IT services use a tailored technique, making sure that protection measures address the one-of-a-kind susceptabilities and operational requirements of each entity.
A tailored safety and security technique starts with an extensive threat assessment, recognizing vital assets, potential risks, and existing vulnerabilities. This analysis enables companies to focus on safety efforts based on their a lot of pushing requirements. Following this, executing a multi-layered protection structure comes to be vital, incorporating sophisticated modern technologies such as firewall softwares, intrusion discovery systems, and file encryption procedures tailored to the company's details setting.
Additionally, ongoing monitoring and normal updates are crucial components of an effective customized approach. By continually analyzing danger knowledge and adapting protection steps, companies can stay one step ahead of potential strikes. Engaging in worker training and recognition programs better strengthens these strategies, making certain that all employees are furnished to identify and respond to cyber risks. With these tailored techniques, organizations can successfully boost their cybersecurity stance and protect sensitive data from emerging hazards.
Cost-Effectiveness of Managed Provider
Organizations progressively identify the considerable cost-effectiveness of managed IT services in today's competitive landscape. By outsourcing IT works to specialized carriers, organizations can decrease the expenses linked with keeping an in-house IT division. This shift makes it possible for companies to allocate their sources extra efficiently, focusing on core service procedures while original site profiting from expert cybersecurity actions.
Handled IT solutions generally operate a subscription version, providing foreseeable monthly prices that help in budgeting and economic planning. This contrasts sharply with the uncertain expenses commonly related to ad-hoc IT services or emergency repair services. MSPAA. In addition, handled solution carriers (MSPs) use access to innovative technologies and skilled specialists that could or else be economically unreachable for lots of companies.
Additionally, the aggressive nature of handled solutions aids reduce the danger of expensive data breaches and downtime, which can lead to significant monetary losses. By investing in managed IT remedies, business not just boost their cybersecurity position yet likewise realize long-term savings via improved operational efficiency and lowered threat exposure - Managed IT. In this fashion, managed IT services arise as a critical investment that supports both financial stability and durable protection
Conclusion
In final thought, handled IT services play an essential duty in improving cybersecurity for companies by executing personalized security methods and continual tracking. The aggressive discovery of risks and routine analyses add to protecting sensitive information versus possible violations.
Report this page